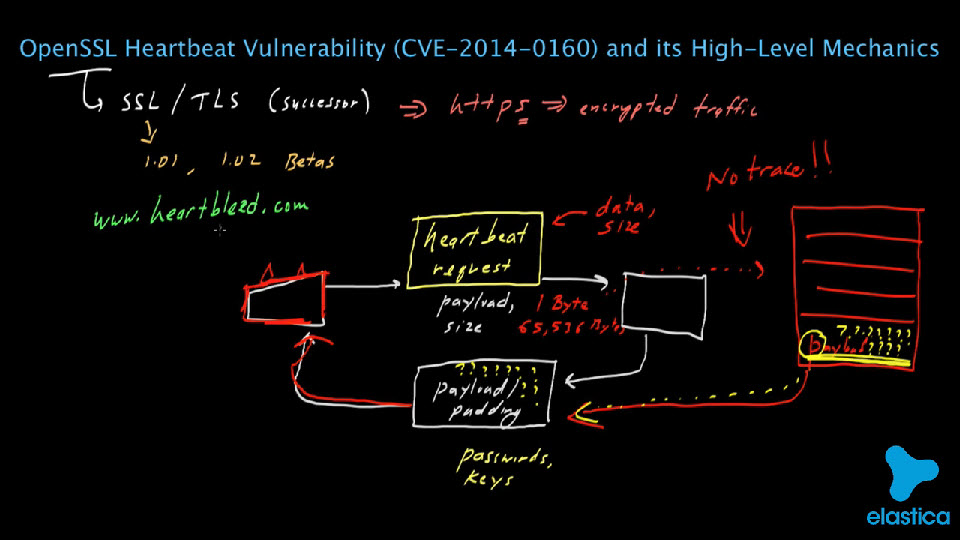
On the internet front, news broke this week of  researchers discovering an widely-used internet security door (an encryption protocol called OpenSSL) that has been left ajar for almost two years now. It is called the ‘Heartbleed’ bug because it draws encryption keys (!) and password information (!) from the back-and-forth sending of encrypted data between a server and a client computer. Hackers using it leave no trace, so it is unknown how widespread its exploitation has been.
researchers discovering an widely-used internet security door (an encryption protocol called OpenSSL) that has been left ajar for almost two years now. It is called the ‘Heartbleed’ bug because it draws encryption keys (!) and password information (!) from the back-and-forth sending of encrypted data between a server and a client computer. Hackers using it leave no trace, so it is unknown how widespread its exploitation has been.
Says internet security expert Brian Krebs on his blog : It is likely that a great many Internet users will be asked to change their passwords this week (I hope). Meantime, companies and organizations running vulnerable versions should upgrade to the latest iteration of OpenSSL (1.0.1g) — as quickly as possible. So the company has to upgrade its OpenSSL, and the users have to change their passwords as well. The problem is, given the growing public awareness of this bug, it’s probable that phishers and other scam artists will take full advantage of the situation. (Sending users fake and infected requests for clicking on a link to changing a password, for example. ALWAYS go directly to the website by typing in the URL or using an established ‘favorites’ link, when changing a password).
Here are Krebs’s 3 Basic Rules for online safety, that should drastically reduce the chances of handing control over of one’s computer to the bad guys.
Rule 1) If you didn’t go looking for it, don’t install it.
Rule 2) If you installed it, keep it updated.
Rule 3) If you no longer need it, get rid of it!